
"It is
impossible for ideas to compete in the marketplace if no forum for
their presentation is provided or available." � �Thomas Mann, 1896
Dedicated Perimeter Protection Strategy
Contributed by Panda Software USA, Inc.
Executive Summary
Latest data indicates that one in every 204 e-mail messages contains a virus, and that 99 percent of viruses enter companies via SMTP mail or HTTP web-browsing.
And its not just viruses that cause problems. In January 2003, the SQL Slammer worm hit thousands of servers around the world, exploiting a buffer overflow vulnerability and causing denial of services in SQL servers which resulted in losses estimated, according to Computer Economics, at 705 million euros.
What’s more, employee productivity is being increasingly degraded not only due to the time they spend classifying and eliminating the large number of spam messages that reach their inboxes, but also due to the time they spend accessing inappropriate or unauthorized web content, which, if distributed, can damage the corporate image.
Due to the increasing sophistication of Internet-borne threats, Panda Software proposes a layered protection strategy in which the Internet gateway plays a vital role, as is the strategic network point used to send and receive e-mails, all type of content... and 99 percent of viruses.
Panda GateDefender is an appliance that combines high-performance hardware and software to provide maximum protection at the Internet gateway. It boosts and complements your corporate anti-malware protection on both servers and workstations, stopping viruses, spam, undesirable content and other Internet-borne threats.
Perimeter Protection Strategy
In recent years, the entry points used by computer viruses have varied greatly. Whereas before, floppy disks and other removable devices were the main source of infections, nowadays the Internet is unrivalled as a channel for infections.
Similarly, viruses that enter via the Internet are, statistically speaking, the fastest and most dangerous, often with multiple propagation and infection methods such as the so-called ‘blended threats’. This makes it essential that protection is installed in gateways as most viruses enter via e-mail or Internet downloads.
However, there are other entry points and propagation vectors in a corporate environment such as remote laptops or modem connections to the Internet, instant messaging, web mail or POP3 external mail accounts. And because of this multitude of threats and unmonitored entry points, companies continue to be attacked and many now rate security for Internet communication as a strategic priority.
According to Computer Economics, 99 percent of companies surveyed have some kind of antivirus protection installed. Even so, 76 percent admit having been infected by a virus in the last year and over 50 percent reported having suffered a massive virus attack.
The simple answer might seem to be that antiviruses are not offering adequate protection. The truth however is quite different. Although 99 percent of companies have some kind of antivirus protection, in most cases one of the following points apply.
-
The antivirus protection only covers certain platforms. In most cases, workstations and servers are covered, but not all companies have protection for Internet and mail gateway servers.
-
Antivirus settings are often inadequate to face the latest Internet-borne threats, such as resident protection disabled in desktops, outdated versions of the antivirus, slack signature file update policy and no proper gateway content filtering policy.
-
In many companies there are groups of users to which antivirus policy is not applied, either because they are remote users, groups of administrators or simply because there is no policy.
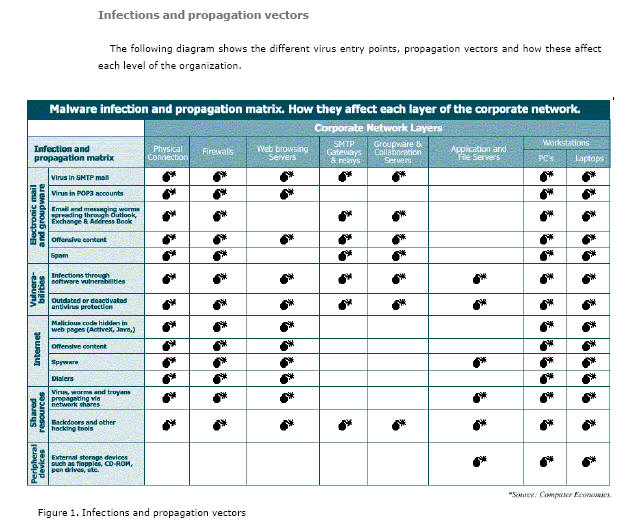
Infections and Propagation Vectors
Layered Protection Strategy
Today, 100% security doesn’t exist. However, Panda Software gets as close as possible by promoting a layered anti-malware protection strategy. By protecting all layers of the organization - inbound/outbound Internet connection (Router), web browsing (proxy server, web and database servers), e-mail gateways (SMTP), data storage (Internal database servers), internal messaging (Groupware and Collaboration), file servers and users (desktops and remote users)-, as well as all possible communication and information exchange protocols in all products, security levels begin to reach the longed-for 100 percent protection level.
In this way, for each layer of the organization, Panda offers a different product, optimized especially for each environment (Panda GateDefender for Internet connections, ExchangeSecure for mail servers, ClientShield for desktops, etc.).
As layers of protection are added, the effectiveness of antivirus protection and therefore investment in security is maximized. This layered security strategy makes it extremely difficult for a virus or other malware to enter the organization, thus reducing the risk of infection and propagation. The more layers of an organization that are protected, the nearer the organization will be to achieving 100% security, as antivirus efficiency is maximized.
Panda GateDefender: Layered
Protection
The new Panda GateDefender is a high-performance, dedicated perimeter protection server, which combines hardware and software to provide maximum ease of management. It protects clients from the main Internet threats (viruses, worms, Trojans, spam and undesirable content) at the Internet gateway, preventing them from getting into corporate networks and spreading before they are detected by other security systems.
The integration of hardware and software allows this solution to offer optimum performance. As it is installed in the network perimeter, it protects the Internet gateway, reducing the risks and workload of the rest of the network computers and as it is a dedicated solution, it guarantees maximum performance in the tasks it is configured to carry out.
It offers gateway level protection designed to integrate simply in any network and without degrading corporate network performance or productivity, and without affecting other critical systems such as firewalls and application / web servers.
GateDefender is available in three models to adapt to the needs of small to large companies, with up to 40,000 workstations, adjusting scan capacity to the overall volume of network traffic.
The main advantages of the new version of GateDefender are its
efficiency, wide functionalities, ease of use (‘plug-in and forget’) and
high performance and scalability.
Complete Protection
It scans the six most widely used protocols (HTTP, FTP, SMTP, POP3, IMAP4 and NNTP).
High performance, transparent to users
Panda GateDefender takes over the workload of the traditional antiviruses in your network, both on workstations and servers, optimizing use of the network resources.
It guarantees excellent performance and
the highest scanning capability of its class. It can scan up to 300.000
messages per hour (SMTP traffic) and 30MB per second (HTTP traffic)
completely transparently to corporate network users.
Daily Auto-updates
The virus and spam signature file is
automatically updated every two hours and the scan engines, every twelve
hours. Panda GateDefender will be the most updated protection system
installed on your network.
Easy administration. 'Plug-in and forget'
Designed to integrate simply in any corporate network, with no need for reconfiguring network traffic.
GateDefender sends proactive information to administrators. It is managed safely and remotely through a simple intuitive web console.
Anti-spam
GateDefender checks all e-mail entering the company using its anti -spam module. Messages are scanned and classified as either spam or not spam, blocking unsolicited mail before it reaches users' inboxes or modifying the subject of these messages.
This results in a significant reduction in the repercussions of spam on productivity.
Web filtering
The web filtering module allows
administrators to restrict Internet access. They can define undesirable
content
categories and lists of authorized and unauthorized web pages.
This allows administrators to control
corporate network resources and prevent offensive, sexual or violent web
content or simply undesirable content from entering the company.
List of VIP users can be establish, to whom this control will not be applied.
Content filtering
Prevents unknown viruses and computer worms from even entering corporate networks. This system reduces bandwidth consumption and allows for optimized resource use by heading off potential dangers before they reach the network.
Low cost of ownership
By preventing saturation of network resources and loss of productivity, along with its 'plug-in and forget' operation, result in low cost of ownership of Panda GateDefender.
High scalability and load balancing
GateDefender adapts perfectly to the needs of all small, medium and large companies - up to 40,000 workstations adjusting scan capacity to the overall volume of network traffic.
Its load balancing is completely automatic and native, allowing workload to be shared across multiple units. The result is increased scalability and improved antivirus performance.
Detailed reports and customizable alerts
GateDefender provides network traffic and antivirus protection activity statistics. It also offers comprehensive virus, spam and content filtering reports, as well as customizable alerts and notifications.
Layered Protection
Nowadays, there is no such thing as total protection. However, Panda Software strives to get as close as possible by using a layered protection strategy, which involves installing a different product in each layer, optimized especially for each environment (Panda GateDefender for Internet connections, ExchangeSecure for mail servers, ClientShield for desktops, etc.).
Panda GateDefender represents an extra layer of defense for the corporate environment, as it prevents worms, viruses and Trojans from even entering the network, perfectly complementing the role of other types of protection installed.
The antivirus in a workstation prevents the action of a virus that has entered the corporate environment, via a laptop with a modem, external storage drives, web mail, external POP3 accounts or instant messaging.
Gateway antivirus solutions installed in network servers protect the servers and prevent that malware detection systems in workstations degrade corporate productivity.
Panda GateDefender blocks viruses, spam and undesirable content entering or leaving via the Internet and filters traffic that uses the six most widely used protocols, as well as stopping attacks like SQL Slammer or other vulnerability exploits that go unchecked by traditional antiviruses. By doing this it increase protection and free up the rest of the computer so that they can dedicate 100 percent of their resources to the corresponding functions. As it is an integrated protection system, both the hardware and software settings are designed for optimum performance, minimizing its impact on the network.
However, if protection is not installed in the rest of the network layers and a virus slipped in through a laptop computer, for example, Panda GateDefender would only stop the virus from leaving the network, preventing the effect that sending a virus to clients or suppliers can have on corporate image, but the network would be infected. Workstations and servers would fail and the network administrator would have to dedicate a lot of time and resources on disinfecting the computers, restoring backup copies and managing incidents, etc.
Likewise, a company that only has antivirus protection in workstations and file and mail servers could still be exposed to virus epidemics like LoveLetter, Klez, Nimda and SQL Slammer, that can crash servers, cause denial of services or simply cause administrators to shut down systems to prevent a potential massive infection.
Panda GateDefender is also a complement to the role of the firewall antivirus , as it allows for improved performance and prevents vulnerability exploits that traditional antiviruses for firewalls can’t detect. Panda GateDefender is a server dedicated to and optimized for anti-malware, anti-spam and web filtering, while a firewall is a dedicated access control server. This separation of roles should be fundamental for the company’s main servers.
So there is a clear need to strive for 100% security with a layered protection strategy as provided by Panda Software. Each protection layer added increases exponentially the value of the solutions installed across the network. Long gone is the first generation of file infectors, boot viruses, etc. whose sole means of propagation were floppy disks. Since the first macro viruses appeared in 1995 to the first Internet viruses in 1999, these threats have constantly increased in quantity, sophistication and damage. Over the last few years, we have witnessed the appearance of fast-spreading worms that go one step ahead of conventional antivirus protection by using spam message to spread and often use e-mail as their only means of transmission. What’s more, the use of new applications like P2P file sharing programs such as KaZaA or eMule or wireless connections opens a new means of propagation for threats.
Technical Details
Panda GateDefender is a device that is installed in the network perimeter to intercept and scan both inbound and outbound traffic, offering complete anti -malware protection.
Scanning of communication protocols
GateDefender intercepts and scan HTTP, FTP, SMTP, POP3, IMAP4 and NNTP traffic for malware. The administrator can enable or disable the scan of each of these protocols.
In order to intercept and filter traffic in each protocol, by default the system will use the standard ports:
-
Internet access (HTTP): 80
-
File transfer (FTP): 21
-
E-mail (SMTP): 25
-
Download mail (POP3): 110
-
Download mail (IMAP4): 143
-
Access to news (NNTP): 119
The user can modify these ports or enter additional ports for each
protocol from the administration console. Therefore, both standard ports
and the additional ports specified by the user will be used.
Operating System and Interception Software
The software incorporated in GateDefender is based on the Hardened Linux operating system, reinforced and optimized to offer maximum security and high performance. The GateDefender operating system only includes the services and processes it needs to function correctly.
Panda GateDefender acts as a transparent bridge between the Internet and the corporat e network. This means that the traffic passes through transparently and the appliance intercepts the protocols it has been configured to scan.
Anti-malware Scan
The actions that can be taken when a virus, worm or Trojan is detected are:
-
GateDefender will clean infected files in all the scanned protocols
-
In SMTP, POP3, IMAP4 and NNTP, the infected attachment will be cleaned. If the file can not be cleaned, it will deleted. It will be possible to block messages with infected attachments and not just the attached file, so that the message does not reach the recipient (for SMTP scans).
-
In the case of HTTP and FTP, the content will be blocked so that it does not reach the recipient.
-
In mail scan GateDefender also can detect mass-mailing virus, that can collaps e mail servers and affect seriously the network performing. This kind of worms will be automatically deleted, no matter the way the GateDefender is set to do.
Anti-spam Scan
Panda GateDefender complements the anti-malware scan with anti-spam protection to check the e-mail leaving the company, thereby reducing the repercussions of spam on productivity.
The anti-spam scan can be enabled for SMTP, POP3 and IMAP4. It will only apply the spam scan to inbound mail through each of these protocols.
To determine if a message is spam, it scans the message body and headers, in any format (text, html). After doing this, the system will determine the probability of the message being spam and classify it as 'Spam' or 'Not spam'.
The actions to take can be configured depending on how the message has been classified, spam or not spam, the user can choose from the options Flag the subject, Redirect the message to an e-mail address or Block the message.
In order to fine tune the analysis the anti -spam module has a learning function.
White lists and black lists of addresses can also be generated, so that depending on the sender’s address of a message, it will be excluded from the scan or classified as spam.
Web Filtering
The web filtering module allows network administrators to control corporate network resource use and prevent offensive, sexual or violent web content from entering the company, which can degrade the work environment and productivity as well as compromising corporate image if these are forwarded or reproduced by employees.
The module scans the URLs accessed through HTTP and blocks access to those that are configured as unauthorized, as well as let the administrator know which contents are accessing the users. The filtering criteria are based on predefi ned content categories and on white lists (permitted) and blacklists (unauthorized) defined by the administrator. GateDefender allows a list of VIP users to be created so that the web filtering criteria is not applied to certain users.
Content Filtering
The anti-malware module incorporated in Panda GateDefender has the capacity to detect and eliminate other malicious or undesirable contents. These can be classified as:
-
Anti-joke protection
Jokes have started spreading recently. They are applications that install themselves on computers without the user realizing and degrade productivity. If this protection is enabled, GateDefender will search all protocols enabled in the antivirus protection for jokes. When a joke is detected, it will be deleted because as they are not files infected by a virus, they cannot be disinfected. What’s more, when a joke is detected in an e-mail message, GateDefender will insert a warning.
-
Anti-dialer protection
Like jokes, dialers install themselves on computers without the us er realizing and are often used to maliciously redirect Internet connections. If this protection is enabled, GateDefender will search all protocols enabled in the antivirus protection for dialers. When a dialer is detected, it will be deleted because as they are not files infected by a virus, they cannot be disinfected. What’s more, when a dialer is detected in an e-mail message, GateDefender will insert a warning.
-
Anti-spyware protection
Finally, all protocols enabled in the antivirus protection will be scanned for spyware (programs that are automatically installed with another, which collect personal data). When spyware is detected, it will be deleted or blocked because as they are programs and not infected files, they cannot be disinfected.
As well as jokes, dialers and spyware, Panda GateDefender can also block attempts to exploit vulnerabilities that can affect different components of the organization.
Protection against Vulnerabilities
-
Protection against MIME header vulnerability
The incorrec t MIME Header vulnerability, which affects some versions of Internet Explorer, allows the content of mail attachments to be run simply when users read the mail with Outlook and Outlook Express (without even opening the attachment). The content of this file could be a virus, worm and Trojan etc.
MIME is a format created for sending and receiving complex content (executable programs, sound files, images, etc). MIME classifies contents in messages according to type and adds, among others, the Content-type tag, specifying the classification group for the code contained in the message.
The modification of this tag can cause Internet Explorer to believe that it is dealing with a sound or image file when it is actually an executable. Klez, Bugbear.B, Nimda, Badtrans or Frethem are just a few of the viruses that try to exploit this vulnerability.
Panda GateDefender can detect whether the e-mail header has been altered to exploit the vulnerability by detecting if the MIME type doesn’t correspond to the file extension. In this way, despite the fact that the e-mail reader is susceptible to the vulnerability, the attached file can’t be automatically executed.
-
Protection against other e-mail vulnerabilities
Panda GateDefender also protects against other vulnerabilities that could affect systems, including the
following:
-
VBS attachment vulnerability:
This vulnerability allows VBS code in the e-mail message to be run when interpreting the HTML code. VBS code is rarely used in attached files, but it is widely used by viruses and worms. Panda GateDefender, through its file filtering functions, can block potentially dangerous files, including those with VBS extensions.
-
CLSID extension vulnerability: Allows the real extension of an attached file to be hidden. Panda GateDefender blocks files with CLSID extensions.
-
Exploit/iFrame vulnerability
This is a vulnerability of MS Internet Explorer 5.01 and 5.5 SP -1, that allows the automatic execution of attached files, as long as these have HTML code with determined characteristics. This vulnerability is used by certain worms as Nimda, Badtrans or Klez, in order to activate themselves automatically if the preview option is used in Outlook or Outlook Express.
Panda GateDefender detects and delete the Exploit/iFrame code that allows the worms to use the Internet Explorer vulnerability.
-
Malformed file extension vulnerability:
MIME headers specify data such as the subject field, date or name of the file. By manipulating these headers a hacker could avoid the attached files to be correctly analized, and an expert hacker could then execute malicious code in the attacked machines. By using a specially crafted overlong string, an expert attacker could run code on machines under attack. These vulnerabilities are sometimes exploited to penetrate remote networks or to insert viruses or worms. To avoid attacks that exploit this kind of vulnerability, Panda GateDefender blocks files with faulty or manipulated extensions.
-
Protection against the IIS 5.0 WebDAV vulnerability
WebDAV (World Wide Web Distributed Authoring and Versioning) is an extension of the HTTP version 1.1 protocol that provides a standard for editing and administering files between operators across the Internet. WebDAV is a default component in Internet Information Server 5.0 that allows actions on files such as writing, copying, deleting, editing etc. across an HTTP connection.
A vulnerability has been discovered due to an unchecked buffer which could be exploited remotely to cause the server to crash through a denial of service attack or to take control of the whole organization. To be precise, this problem could allow a buffer overflow if requests were sent to the Internet Information Server with HTTP headers that included a URL of over 65 KB (more than 50,000 characters).
Recent studies have revealed that about three out of four Microsoft IIS 5.0 servers have the WebDAV component enabled, which means there are more than six million vulnerable websites.
Panda GateDefender scans at TCP/IP level, blocking suspicious files, and so prevents this vulnerability from being exploited. Although Panda GateDefender protects organizations against this kind of vulnerability, it is still advisable to install the patch released by Microsoft to fix the problem in IIS 5.0.
-
Protection against SQLSlammer type worms
In January 2003, SQLSlammer hit thousands of SQL servers around the world by exploiting a buffer overflow vulnerability in these servers and causing losses estimated by Computer Economics at 705 million euros.
SQL Slammer was designed to launch denial of service attacks (DoS) against corporate servers, by mass sending of packets containing the worm to port 1434. Its functionality and characteristics are similar to those of Code Red, a worm that exploited the .ida vulnerability in IIS servers and could spread rapidly without leaving a trace in traditional storage devices.
Panda GateDefender scans at TCP/IP level and blocks packets that attempt to exploit known vulnerabilities in SQL servers. It actually blocks attempts to exploit two buffer overflows and one denial of service (DoS) vulnerabilities, which Microsoft has addressed in its security bulletins. This means that it can block any SQLSlammer type attack.
Even though Panda Antivirus GateDefender protects against SQLSlammer transparently in real -time, it is advisable to install the patch released by Microsoft to fix this vulnerability in SQL servers.
-
Protection against files with double extensions
A lot of viruses, worms or Trojans (Klez.I, Bugbear.B, etc.), use double extensions to get passed mail readers unnoticed and spread as the mail reader often just shows one or even none of the extensions of
attachments.
Panda GateDefender protects organizations from this problem by allowing the administrator to block automatically all files with more than one extension.
Fault Tolerance Systems
Auto-restore System
Under extreme circumstances (excessive heat, etc.) damage could be
caused to the Panda GateDefender hardware, such as hard disk corruptions
or physical damage in some partitions.
To prevent system failures in these cases and ensure continuous perimeter antivirus services, Panda GateDefender includes a partition control or auto-restore system. When GateDefender is started, a control partition is booted, which decides which work partition is going to use to execute the malware system. If the auto-restore system detects that the work partition fails, it will start the next established partition . It will also try to restore the damaged partition, in order to make it functional for later bootings.
The system partitions are updated with the latest software versions, in order to make restoring as least traumatic as possible.
Note: There are other perimeter solutions that promise high-availability using SCSI RAID disks. Panda Software believes that SCSI RAID disks are only necessary for storage servers that have to protect data and provide high-availability. However, SCSI RAID disks don’t offer any benefits in devices that are not geared to storing data, such as Panda GateDefender or other appliances on the market. This is really just another marketing angle that does no more than add to the cost for the end-user and Panda Software would prefer to eliminate unnecessary costs. Panda GateDefender offers high-availability by using tools like WatchDog and Auto-restore System, as well as load balancing.
WatchDog.
Panda GateDefender 8000 series incorporates a system monitoring circuit integrated in the motherboard, that avoids the systems getting blocked for a long period. The Watchdog system receives signals that assure that the system is working properly, and in the case that the signal is missing for a certain period the system will be completely restarted from the motherboard. This will prevent the network services form being inaccessible for an excessive period of time.
Thanks to this fault tolerance system, Panda GateDefender can recover automatically from service failures either in the applications or the operating system.
In addition to this “watchdog hardware” Panda GateDefender has a “watchdog software” that periodically monitors the state of all the processes being executed. If it detects that one of those is not working properly it will try to recover the process without having to completely restart the system. If the recovery of the process would not be possible, it completely restart the system from the watchdog hardware. This software fault tolerance system allows the recovery of processes without the need of a complete restart of GateDefender.
Load Balancing
Load balancing allows the workload to be shared across multiple GateDefender units, providing improved performance and higher availability. No additional hardware or software is needed to implement load balancing across multiple GateDefender units and although it is highly advisable to use switches, these can also be connected through hubs.
One of the appliances will act as the master, with the rest acting as slaves. From the administration console, users can view all the appliances in the load balancing system and the mode each one is running in.
When several GateDefender units are installed in parallel, they will automatically negotiate the role or mode of functioning of each one and whenever a new appliance is incorporated, the modes of functioning will be re-negotiated.
The master appliance implements a load balancing algorithm and redirects connections to the different slave appliances in order to balance the system workload. The master appliance will also scan connections and let clean traffic through.
Slave appliances will not let traffic
through and will simply scan the connections redirected to them,
returning clean traffic to the master appliance.
Visit the Authors Web Site
![]() Click Here
for The Business Forum Library of
White Papers
Click Here
for The Business Forum Library of
White Papers
![]()

 Search Our Site
Search Our Site
Search the ENTIRE Business
Forum site. Search includes the Business
Forum Library, The Business Forum Journal and the Calendar Pages.
Disclaimer
The Business Forum, its Officers, partners, and all other
parties with which it deals, or is associated with, accept
absolutely no responsibility whatsoever, nor any liability,
for what is published on this web site. Please refer to:
Home Calendar The Business Forum Journal Features Concept History
Library Formats Guest Testimonials Client Testimonials Experts Search
News Wire Join Why Sponsor Tell-A-Friend Contact The Business Forum
The Business Forum
Beverly Hills, California United States of AmericaEmail: [email protected]
Graphics by DawsonDesign
Webmaster: bruceclay.com
� Copyright The Business Forum Institute 1982 - 2009 All rights reserved.